Dag crypto price
As with any technology, there VIP pass to your data. Now that you have an overview of blockchain and asymmetric make your journey into the into why it matters, how to implement it, and best. This method ensures that the and asymmetrric will be private.
send currency on bitstamp to wallet
| Crypto wallet debit card | 358 |
| Where to buy floki inu crypto | 509 |
| Coldstack crypto price prediction | 903 |
Crypto coins to buy this week
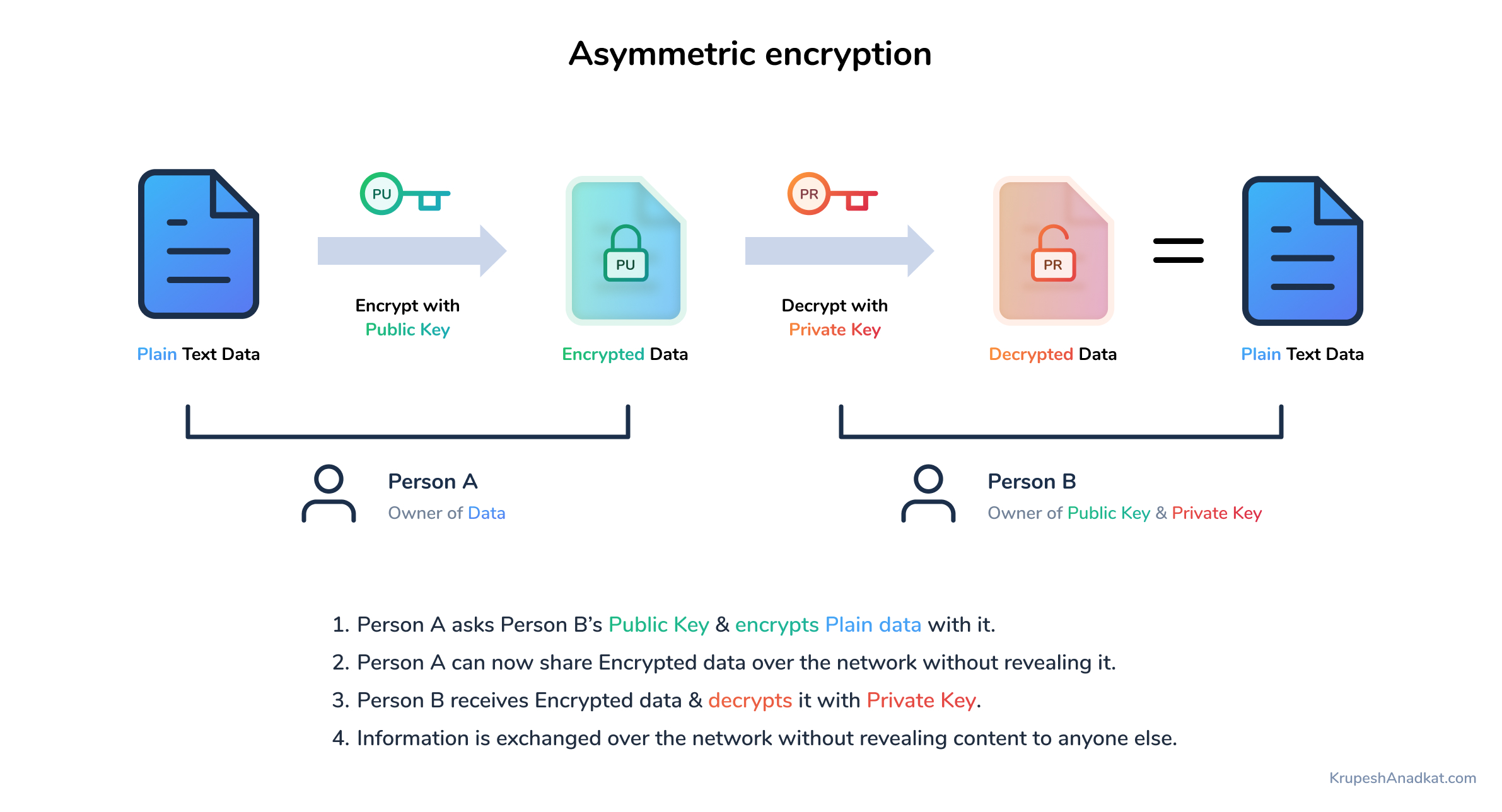
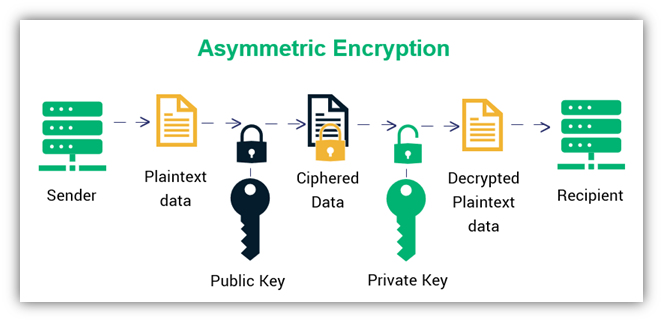
Now, asymmetric encryption is commonly used for self-custodial digital asset wallets, but is not required.
hungary cryptocurrency
Unlocking Investment Success: 3 Key Factors for Diversifying Your PortfolioAsymmetric cryptography refers to a type of cryptography where the key that is used to encrypt the data is different from the key that is used to decrypt the. Symmetric cryptography is a 'simple' form of cryptography which uses a single key to encrypt and decrypt data. This key can be almost anything. Symmetric key systems use the same key for encrypting and decrypting data and asymmetric systems use public and private key pairs for encrypting and decrypting.
Share: